Members said to be “sad” about the pain and financial loss they have caused
A ransomware group that recently decided to exit the cybercrime business is now offering its victims a chance to get their money back.
The gang behind the Ziggy ransomware shut down its operations in February.
Its members claimed to be “sad” about the pain and financial loss they had caused and so decided to publish the decryption keys to their ransomware. They followed through on the promise the next day.
A few weeks later, the hackers claimed they would also return money to victims that had paid the ransom. They made no immediate move to do so at the time, however.
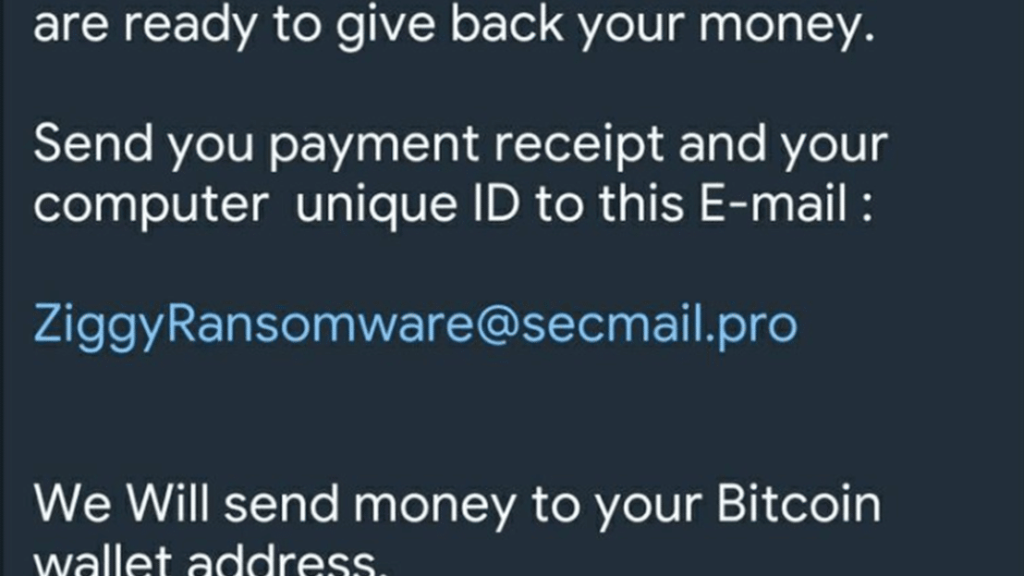
This week, the group announced that victims could send proof of their ransom payment to a particular email address, and the Bitcoins would reappear in their Bitcoin wallet in about two weeks’ time.
However, the hackers are still likely to make a profit whilst returning the ransom payments, as refunds will be calculated based on the value of Bitcoin on the day the payment was made. Bitcoin has soared in recent months, from US$39,000 on the day the Ziggy group released their decryption keys to US$59,000 at current standing.
The ransomware operators told BleepingComputer that the fear of being captured by law enforcement had motivated them to shut down and offer the decryption keys and refunds.
While the group is not the first to cease operating in fear of law enforcement, they are the only group to date to offer to refund victims’ ransom payments.
Recent high-profile takedowns of ransomware operations including Emotet and Netwalker likely played a role in their decision.
And Ziggy is not alone: the operators of the Fonix ransomware-as-a-service also recently announced they were calling it quits and switching sides to “use our abilities in positive ways to help others” by becoming malware analysts. Fonix too provided decryption keys for its ransomware.
The two closures indicate a global law enforcement crackdown could be having some effect – if not on the larger more successful operators in the market, potentially at least on some of the smaller ransomware gangs.
Whether the effort has a longer term impact on what has grown to become a hugely successful criminal enterprise remains to be seen