The REvil ransomware group has fully resurfaced, is attacking new victims and posting stolen files on a data breach site.
Since 2019, the REvil ransomware operation, nicknamed Sodinokibi, has been conducting attacks on companies all around the world, demanding million-dollar ransoms in exchange for a decryption key and the prevention of stolen files from being leaked.
During its tenure, the gang has carried out numerous attacks on well-known companies such as JBS, Coop, Travelex, GSMLaw, Kenneth Cole, Grupo Fleury, and others.
“Unfortunately, the Happy Blog is back online,” Emsisoft threat researcher Brett Callow tweeted.
REvil’s Disappearance
After their biggest attack, REvil shut down their infrastructure and completely disappeared. The Kaseya VSA remote management platform was the target of a major attack on July 2nd that affected 60 managed service providers and over 1,500 enterprises using a zero-day vulnerability.
On July 13th, 2021, the REvil gang abruptly ceased operations, leaving many victims in the dark with no method to decrypt their information.
Researchers and law enforcement suspected that REvil would rebrand as a new ransomware organisation at some point after their shutdown.
REvil’s Return
Nevertheless, the REvil ransomware group returned this week under the same name, much to our surprise.
Tor’s payment/negotiation and data leak sites reactivated and became available on September 7, over two months after they went down. It was possible to engage with the ransomware group again a day later.
All prior victim’s timers were reset and their ransom demands had remained the same when the ransomware gang ceased down in July.
According to ‘REvil’, a new spokesman of the ransomware operation, the group temporarily shut down after believing Unknown (REvil’s previous spokesman) had been arrested and systems compromised on September 9th.
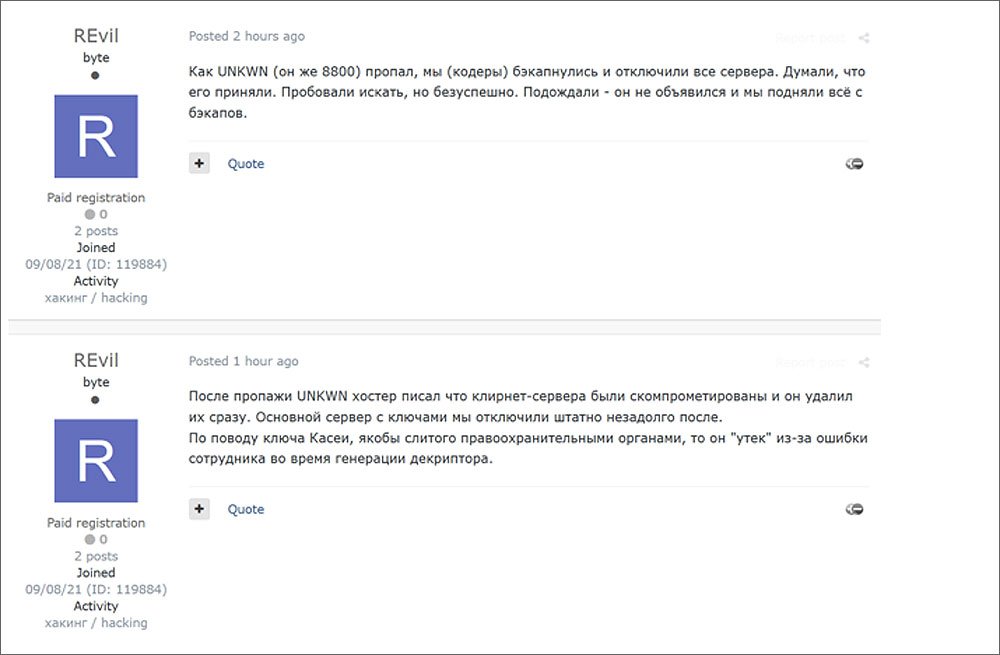
This translation of these posts can be read below:
“As Unknown (aka 8800) disappeared, we (the coders) backed up and turned off all the servers. Thought that he was arrested. We tried to search, but to no avail. We waited – he did not show up and we restored everything from backups.
After UNKWN disappeared, the hoster informed us that the Clearnet servers were compromised and they deleted them at once. We shut down the main server with the keys right afterward.
Kaseya decryptor, which was allegedly leaked by the law enforcement, in fact, was leaked by one of our operators during the generation of the decryptor.”
– REvil
While we may never know the true reason for the disappearance or how Kaseya gained the decryption key, the most important is to know is that REvil is back to targeting corporations all over the world.
REvil’s skilled affiliates and ability to perform sophisticated attacks could result in devastating business outcomes. It’s recommended that all network admins and security professions become familiar with expert cybersecurity tactics and techniques, especially if employees are working remotely.




