Aussie banks seem hard hit, but mystery surrounds how the cards were compromised
Key takeaways
- A new criminal carding marketplace has recently gone live
- Some one million stolen cards were revealed
- Of some 400,000 cards analysed to date, some 80,000 relate to Australian banks
- But it remains a mystery as to how these cards were compromised, with a possibility that the banks themselves may have been compromised given the huge number in play.
A threat actor is promoting a new criminal carding marketplace by releasing one million credit cards stolen between 2018 and 2019 on hacking forums, including cards belonging to customers of Australian banks.
Carding is the trafficking and use of stolen credit cards. These credit cards are stolen through point-of-sale malware, “magecart attacks” on websites, and information-stealing trojans.
These stolen credit cards are then sold on criminal carding marketplaces where other threat actors purchase them to make online purchases or buy hard-to-trace prepaid gift cards.
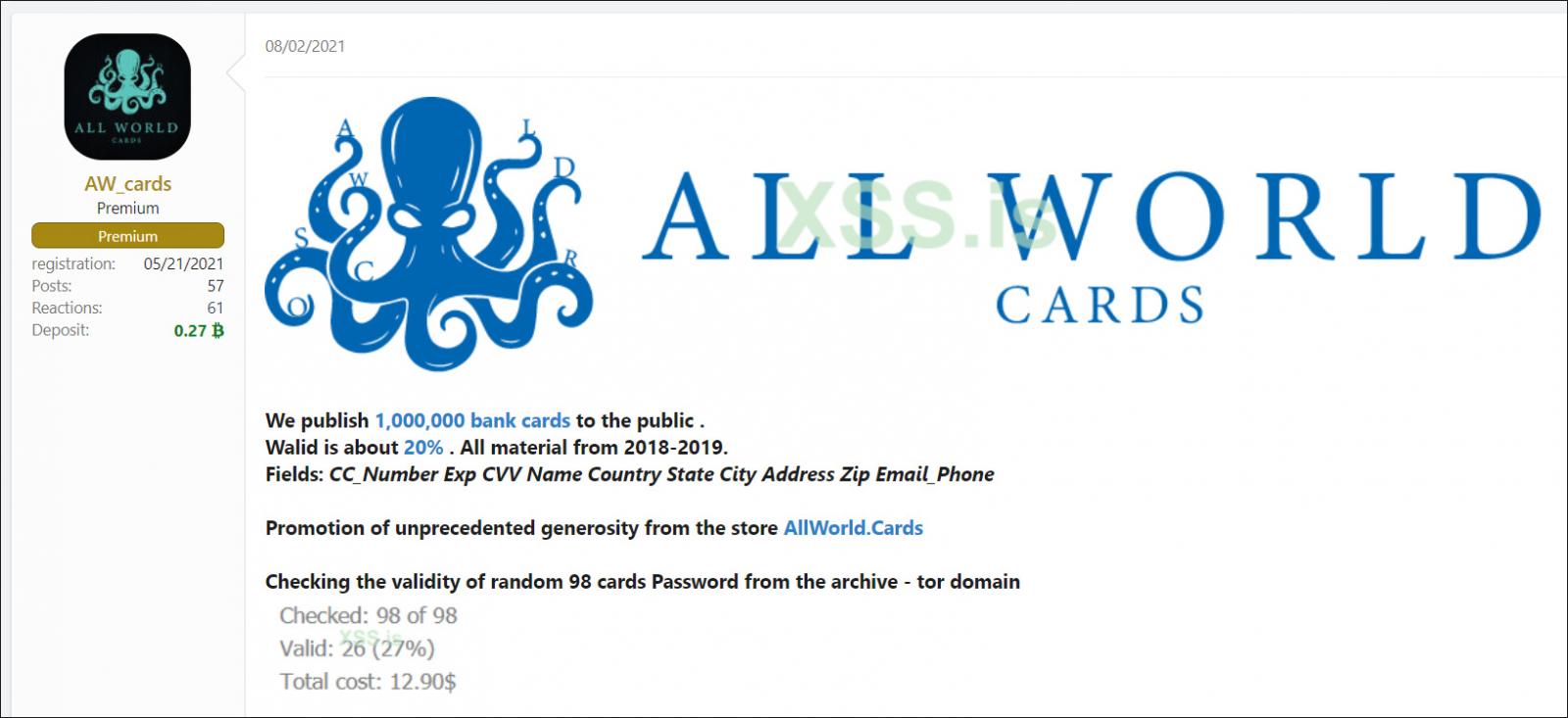
Last week, a new criminal carding marketplace called AllWorld Cards posted to numerous hacking forums where they leaked one million credit cards for free.

According to the forum post, these credit cards were stolen between 2018 and 2019.
Large number of cards still active
The threat actor states that a random sampling of 98 cards showed approximately 27% of the cards were still active.
However, a report by Italian security firm D3Labs shows that 50% are still valid, a far more significant amount than initially indicated.
“At present, the feedback returned to our analysis team is still limited, but they are showing an incidence close to 50% of cards still operational, not yet identified as compromised.” reported D3Lab in a blog post about the leak.
Cybersecurity firm Cyble also analysed the credit card dump and determined that the leak contains:
- Credit Card Number
- Expiry Date
- CVV
- Name
- Country
- State
- City
- Address
- Zip codes
- Email / Phone

Australian banks among those hardest hit, but how?
Cyble has only analysed 400,000 cards so far, and already there is some concerning news.
Australia is among the worst hit of countries, ranking 4th in the count so far with some 80,000 cards out of the 400,000 analysed.
This should be hugely concerning news to the respective banks. The following Australian banks all feature in the list:
- Commonwealth Bank: 24,158
- ANZ: 16,677
- Westpac: 11,381
- NAB: 6,230
- ING: 1,946
- Bankwest: 696
You should also review your credit card statement thoroughly to check for historic fraudulent charges and future charges.
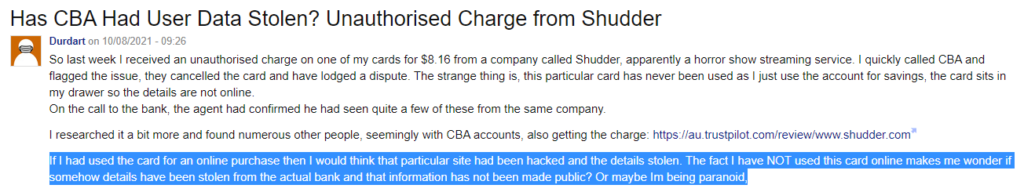
On consumer circles and on internet forums, there has been plenty of chatter about the leak, with Australian consumers rightly concerned.
The greatest concern surrounds how exactly the cards were compromised. The high number of credit cards compromised doesn’t correlate with the normal ‘phishing’ methods used by threat actors to get credit card numbers, or a data breach relating to a retailer.
It is thus possible that the banks themselves have been compromised at some point in the past.
On popular website Ozbargain, users speculated about how this may have happened, with one mentioning that the card compromised for them was one they had never used online!
What to do? Tips to avoid paying the price
Whether you’ve been caught up in this incident or not, there are a few key things we all need to do to ensure that we are protected from a credit card risk perspective.
Below, I share some of the most critical of these measures that we should take as best practice at any given time, regardless of whether we’ve been impacted to date by an incident:
- Change your online banking password – If you are like 99% of people, you probably have not changed your online banking password in a while, and there is strong chance you have reused the same password across other accounts too. It’s time to change it to a unique and more secure password. Don’t like to remember long and complex passwords? Then consider using a password manager such as 1password or keepass.
- Enable Multi-factor authentication – This is a way to confirm your identity by requiring additional verification steps such as through SMS or by giving you a hardware token. Most banks offer and encourage MFA and so they should. If you can, turn on MFA for all your critical needs, not just banking.
- Monitor your transactions and sign up for alerts – Keep a close eye on your statements and consider enabling alerts on transactions over certain amounts if the bank offers this. This will mean every time there is a transaction from your account you get pinged and if something seems off, you can instantly take action.
- Review your limits – Most banks offer safety features such as enabling you to limit the amount that can be withdrawn from your account in a day and to stop any international online or offline shops from charging credit cards. Turn these limits on and set them up so you have more control over your account.
Together, these measures can make a huge difference. They can be the difference between needless loss of thousands of dollars (if not more).




