Google has been all over the news in Australia for other reasons recently, but recent revelations about its popular Chrome browser won’t go down well with many users.
New details have emerged about a vast network of rogue extensions for Chrome and Edge browsers that were found to hijack clicks to links in search results pages to URLs leading to phishing sites and ads.
Experientially, this is a problem well known to many users. You’ve probably installed a Chrome extension at some point only to have it take you to weird and wonderful places around the internet. This analysis confirms what many have experienced, but brings to light the extent of the problem.
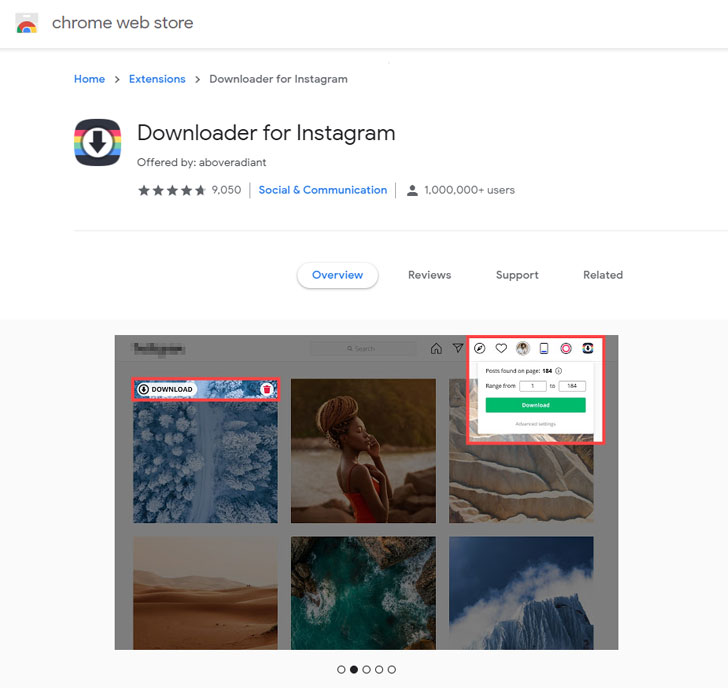
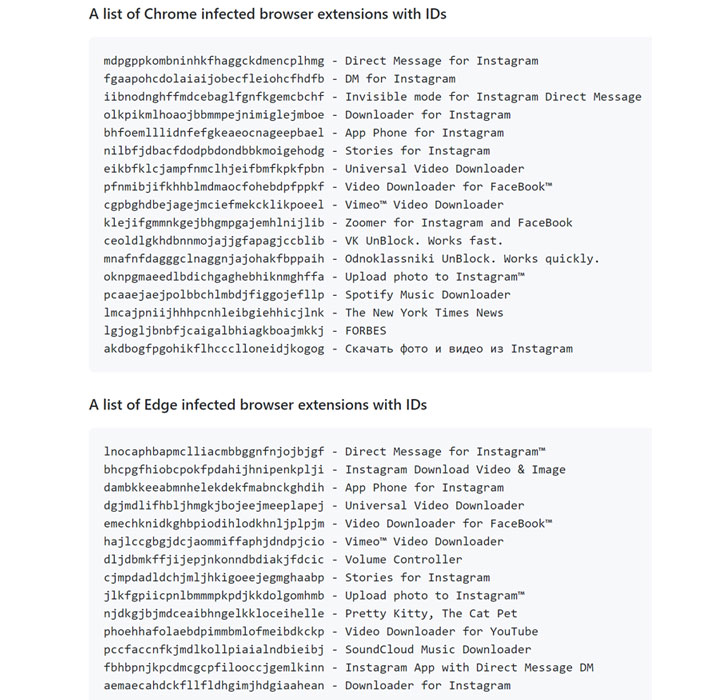
Collectively called “CacheFlow” by Avast, the 28 extensions in question — including Video Downloader for Facebook, Vimeo Video Downloader, Instagram Story Downloader, VK Unblock — made use of a sneaky trick to mask their true purpose.
All the backdoored browser add-ons have since been taken down by Google and Microsoft as of December 2020 to prevent more users from downloading them from their official stores.
According to data gathered by Avast, the top three infected countries were Brazil, Ukraine, and France, followed by Argentina, Spain, Russia, and the U.S.
The CacheFlow sequence in question began when users downloaded one of the extensions in their browsers . Upon installation, the extensions would send out analytics requests resembling Google Analytics to a remote server, which then beamed back a specially-crafted Cache-Control header containing hidden commands to fetch a second-stage payload that functioned as a downloader for the final JavaScript payload.
This JavaScript malware amassed birth dates, email addresses, geolocation, and device activity, with a specific focus on collecting the data from Google.
In the final step, the payload injected another piece of JavaScript into each tab, using it to hijack clicks leading to legitimate websites, as well as modify search results from Google, Bing, or Yahoo to reroute the victim to a different URL.
The extensions not only avoided infecting users who were likely to be web developers — something that was deduced by computing a weighted score of the extensions installed or by checking if they accessed locally-hosted websites (e.g., .dev, .local, or .localhost) — they were also configured to not exhibit any suspicious behaviour during the first three days post-installation!
The Avast analysis concludes that the myriad tricks employed by the malware authors to escape detection may have been a crucial factor that allowed it to execute malicious code in the background and stealthily infect millions of victims, with evidence suggesting that the campaign may have been active since at least October 2017!
This incident is yet another example of the level of sophistication threat actors are deploying through creative and innovative means to reach their objectives.




