What is Daxin?
Daxin is a malicious Windows kernel driver with extensive communication capabilities, allowing it to transmit messages through infected systems and communicate with legitimate services on target networks via tunnelling.
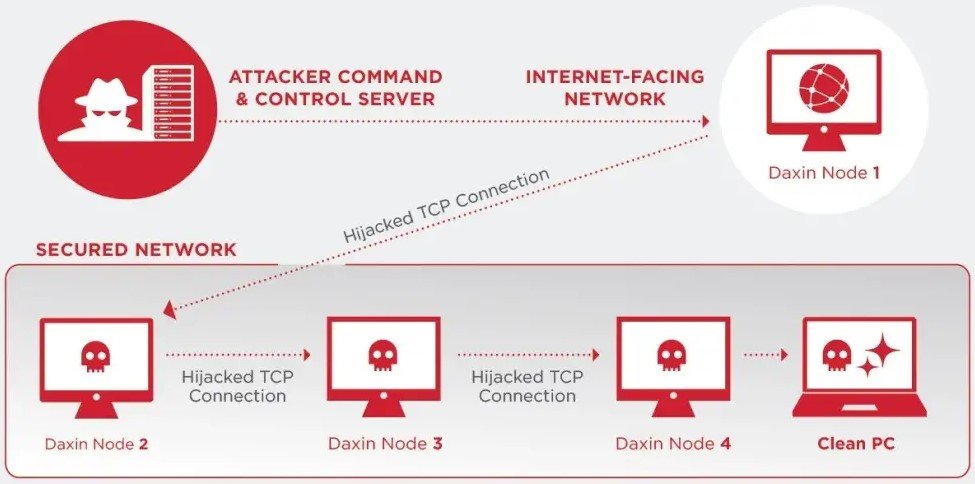
Daxin circumvents strict firewall regulations by hijacking genuine network transmission control protocol (TCP/IP) connections and looking for specific patterns that trigger digital key exchanges for encrypted traffic sessions.
The backdoor can read and create files on infected machines, as well as launch and interact with them invisibly.
While Daxin was used in attacks as late as November 2021, earliest samples trace back to 2013, with all the advanced characteristics that it currently contains.
Although unconfirmed, speculations that Daxin is based on earlier malware, Zala or Exforel, which was used by the same threat actor in 2009.
Who’s being targeted?
Daxin’s victims included high-level, non-Western government institutions in Asia and Africa, including Ministries of Justice.
Afflicted organisations in the US have been notified, but Daxin infections have been reported all over the world, which the US government is assisting in notifying.
What is being done?
The malware’s findings have been shared with US government security agencies that are collaborating under the Joint Cyber Defence Collaborative.
“It’s something we haven’t seen before,” said Clayton Romans, associate director of the US Cybersecurity Infrastructure Security Agency (CISA).
“The capabilities of this malware are remarkable, and it would be extremely difficult to detect without this public research,” said Neil Jenkins, chief analytics officer at the Cyber Threat Alliance.




