The Snake password-stealing trojan is being employed by an increasing number of cybercriminals, making it one of the most used malware families in attacks.
Snake has only been active since November 2020 and is not related to the previous ransomware operation of the same name.
Researchers from Cybereason have investigated how popular malware operates.
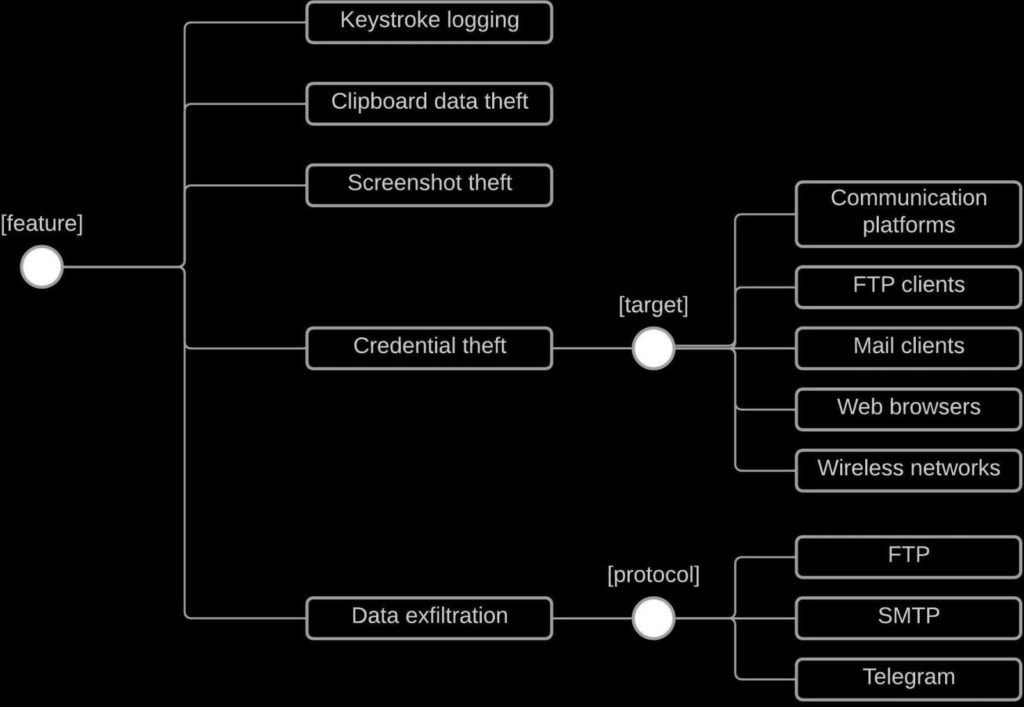
Snake’s Malicious Features
Snake is already being sold on dark web sites for as little as $25, which could explain the increase in its use.
Snake is mostly used in phishing efforts, when it is installed via malicious email attachments or by drop sites accessible by clicking on email links.
Snake, when installed on a computer, can collect passwords from over 50 applications, including email clients, web browsers, and instant messaging services.
Snake has been known to target the following programs:
- Discord
- Pidgin
- FileZilla
- Thunderbird
- Outlook
- Brave browser
- Chrome
- Edge
- Firefox
- Opera
- Vivaldi
- Yandex
According to a prior HP investigation, threat actors may utilise geolocation data to restrict installation based on the victim’s country.
Other characteristics include the ability to steal operating system data, memory space information, geolocation, date-time information, IP addresses, and more.
Avoiding Detection
Snake bypasses antivirus defences by eliminating the associated programs and even disables network traffic analysers like Wireshark to evade detection.
Snake then adds itself to the Windows Defender exclusion list, allowing it to execute dangerous PowerShell commands undetected.
Snake creates a scheduled job and modifies a registry key to be executed when a user enters Windows in order to establish persistence.
It’s worth noting that Snake allows its operators to choose which capabilities to enable the virus during the packing stage.
By minimising the use of features in targeted attacks, they can remain undetected.
Lastly, Snake uses either an FTP or SMTP server connection or an HTTPS POST on a Telegram endpoint to exfiltrate data.
Snake’s ability to perform phishing attacks could result in devastating outcomes. It’s recommended that all individuals, network admins and security professions become familiar with expert cybersecurity tactics and techniques, especially for remote workers.




