What’s Different About This Attack?
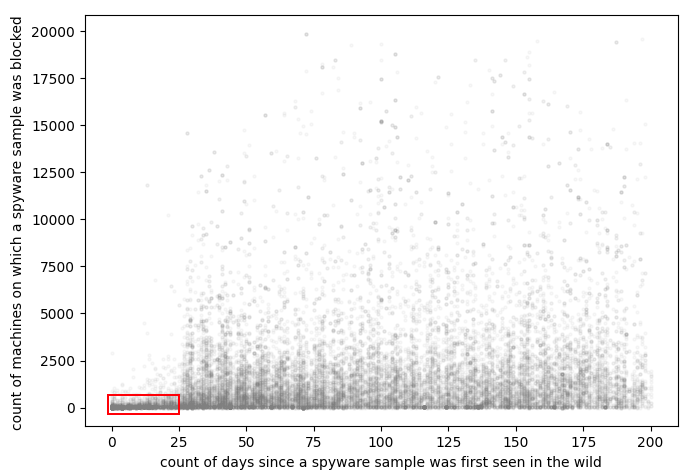
Spyware attacks are typically active for months, but in this case, the threat actors have decided that swapping the spyware every 25 days or so reduces their chances of detection.
Following a successful attack in which credentials are stolen, they often move on to sell the credentials on Darknet marketplaces, with prices varying depending on the sort of access and the firm infected.
AgentTesla/Origin Logger, HawkEye, Noon/Formbook, Masslogger, Snake Keylogger, Azorult, and Lokibot are examples of commodity malware used in assaults.
The threat actors also use the SMTP-based communication protocol to exfiltrate data to the threat actor’s command-and-control (C2) server.
This is unique because, unlike HTTPS, which is the most common way for spyware campaigns to communicate with one another, SMTP is a one-way channel that caters to data theft and thrives on simplicity and its ability to blend in with regular network traffic.
Cybersecurity in the Industrial Sector:
With remote working becoming more widespread in many organisations, cybersecurity has been thrust into the spotlight more than ever in the previous year. While there is always concern about end-user devices, there is also growing anxiety in the industrial sector.
Advanced approaches to manufacturing and supply chain management increasingly rely on data collecting, data analysis, and technology connectivity. These connectivity points, combined with an increase in the number of attacks on manufacturing facilities by hackers and other bad actors, require new approaches and increased diligence to avoid downtime and intellectual property loss.
What Can Be Done?
The protection of the industrial sector, more than any other industry, needs a proactive approach to cybersecurity to test their parameters, educate employees about cyber-risks, ensure compliance and uncover security vulnerabilities.




